How to Select an Enterprise Mobility Management Platform
End users are excited about the tablets and smartphones they purchase for personal use. So it is no surprise that employees want to use these devices at work too. This may be a boon to productivity, but it also raises the mobile security and management bar for IT managers. One way to stay ahead of the bring-your-own-device (BYOD) trend is through the adoption of an enterprise mobility management (EMM) platform.
The fast-evolving nature of mobility demands that a chosen management platform be flexible enough to respond capably to the shifting winds of the market. Look for solutions that assist with the following best practices when evaluating the many EMM platforms available today.
Enforce Basic Device Security
Security is the first item that an EMM solution should address. Make sure device-level encryption is enforced for each device that connects to the network, and enforce a PIN or password requirement for all devices. These are good initial lines of defense against any attempted brute force attacks on the mobile endpoint.
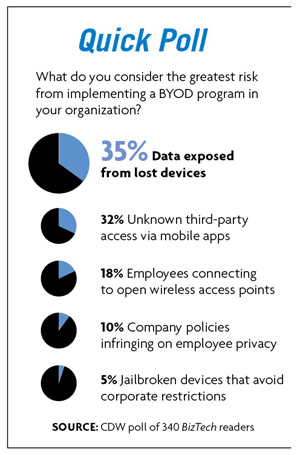
Next, make sure remote lock and wipe are enabled. This allows IT staff to respond quickly in the event of a lost tablet or smartphone. Be sure to let users know that a lost device will be locked, then wiped if it is still missing after two weeks have passed. This will greatly increase the number of lost devices reported, as users will feel that they have enough time to find their phone and recover not only their company’s valuable data but the pictures of their kids and cats as well.
Create a Company App Store
Companies that currently don’t have an app store are not alone. Gartner estimates that by 2017 less than 25 percent of organizations will have one. There are great reasons, however, for a business to join this minority. App stores, available through most major EMM platforms, provide a single point of entry for employees to access all company apps. These can be custom apps built specifically to meet business objectives or off-the-shelf, third-party apps.
The percentage of BYOD access that is inadequately managed or not managed at all by organizations
SOURCE: BYOD Survey (Ovum, September 2012)
Because app distribution is controlled by the company, the app store also provides a seamless method for app whitelisting (approving) and blacklisting (blocking). This allows IT staff to quickly neutralize and quarantine apps that are discovered to have undesired functionality or security holes, as well as publicize those that are considered company standard.
Also, app stores discourage users from buying their own apps and expensing them. This allows businesses to retain negotiating power for volume app licensing and avoids maverick purchases.
Wrap and Containerize
Mobile app management now makes it possible for apps to run in an individual, secure container that is deployed to each employee’s mobile device. This enables organizations to apply policy on a per-app basis, on the fly and without any code changes. For example, if a business wants users to be able to access the company’s instance of Box via mobile devices, but with the “share” feature disabled, app wrapping allows that. If you want to create geofencing, whereby an app runs in one physical location but not another, app wrapping can do that too.
This method of applying policy around an app on a per-app basis is far superior to the more draconian method of creating two separate containers or personas on employees’ mobile devices. Separate personas force the user to switch between two different modes on a smartphone, for instance, usually causing nothing but frustration to the end user. App wrapping, on the other hand, provides seamless integration with the mobile OS environment and allows users to quickly switch between work and personal tasks without having to switch contexts.
Measure and Analyze
By understanding utilization and trends, companies can create a smooth running environment for mobile devices. Again, many EMM platforms offer analytic tools that can help organizations get a firm grasp on employee usage and decide how to plan for the future.
When choosing what to analyze, a good place to start is user engagement: How many users? What is the retention rate of users with each app? Are some apps used for several days and then abandoned? Who are the most active users? How long are sessions? Managers can also examine mobility management costs per user, wireless network usage and staff support per user.
Adjust Attitudes
Mobility is as much a cultural as technical change. Part of running a business smoothly comes from understanding the changes that are taking place in and around IT and making sure the proper adjustments are put in place. This is especially true of BYOD. And as end-user expectations and technical adeptness grow, it is important to not hold back those employees who want to excel. This means letting go of the old IT notion of command and control and being willing to view IT’s role in the organization more as a systems integrator and enabler.
Attitudes toward tech support must change as well. When it comes to working with people and their mobile devices, it is best to help employees help themselves. Users today are very attached to their smartphones and tablets. They are the last things they look at before bed and the first when they arise. Users will go the extra step to understand their technology. Use that to the company’s advantage as part of a mobile management strategy.
Mobility continues to evolve at breakneck speed. With the help of a good mobility management platform — and a positive partnership with end users — companies can keep up with these changes by staying mobile-savvy.










