Hacker Profiles: Meet the New Kids on the Block [#Infographic]
While there’s been a fear of hackers on the web since the “You’ve got mail” days, recent front-page attacks point to an increase in the volume and precision of cyberattacks, which should alarm enterprises of all sizes.
This is especially true because more businesses have begun to digitize sensitive information, such as financial records.
As BizTech highlighted back in March, an increasingly paperless world has changed the way business treats data:
The benefits of a move to digital documents from physical paper include reduced costs, improved efficiency and instant access to documents. But the path to paper’s dematerialization is not without its twists and turns. If we are to achieve a paperless future, then we need secure and scalable methods of data authentication.
The first line of defense against system compromise is knowledge. Being aware of the threats you face can help the data hemorrhage before it starts.
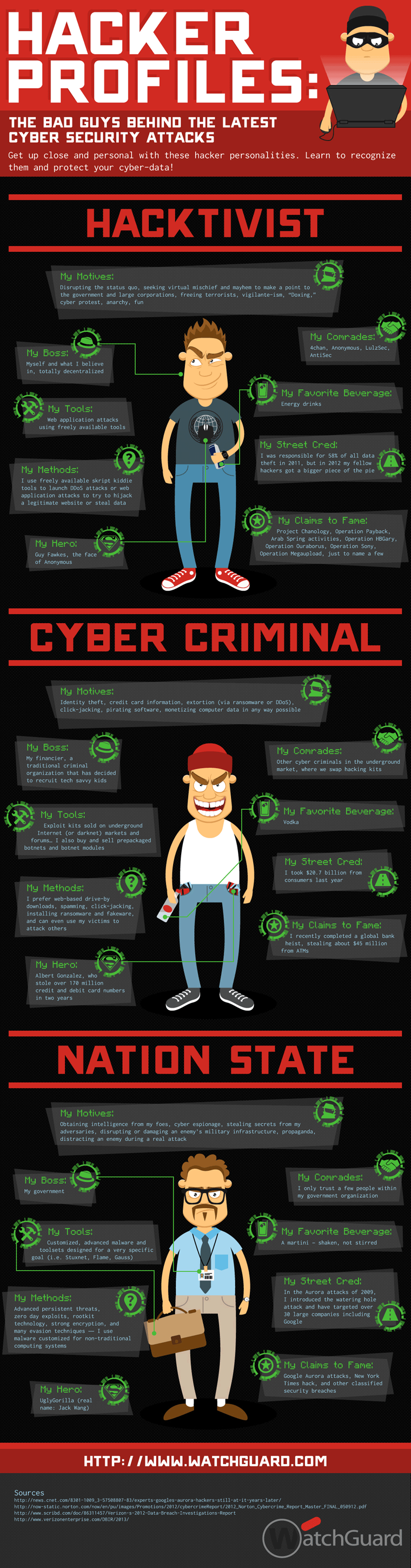
WatchGuard, a provider of business security solutions and hardware, recently released an infographic of the 3 Most Dangerous Types of Hackers: the hacktivist, the cyber criminal and the nation state.
"We no longer live in a world of fame-seeking hackers, script kiddies, and cyber criminals—there are some new kids on the block. It's important to understand these motive and profile changes, since they dictate what each type of hacker is ultimately after, whom they target, and how they tend to do business," said Corey Nachreiner, director of security strategy at WatchGuard, in a recent blog post. "Knowing these things can be the key to helping you understand which of your resources and assets need the most protection, and how you might protect them."
Top data vulnerabilities include denial-of-service (DoS) attacks, spam, customized malware and cyber espionage. How deep have the hackers hit? According to WatchGuard, cyber criminals stole $45 million from ATMs in a global bank heist.
Using these hacker profiles, businesses can take proactive steps to evaluate system security and prioritize protection services to address hackers who have these unique motives. Anticipating an attack before there is an actual problem is the best way forward.
Check out the full WatchGuard infographic below for more information.