BYOD and MDM: Personal and Professional Data Working in Harmony
The term “motion” has a specific legal meaning in a law firm. But in the offices of Dowling Aaron, it also defines how attorneys are able to work: in motion.
The law firm’s 50 attorneys work on the go. They might be at a courthouse, meeting with clients away from the office or working from home in the evening. Using their own smartphones and tablets to access e-mail, draft briefs and leverage the firm’s legal applications is a major convenience.
“Our attorneys want to be able to work 24x7, and each of them has at least one mobile device,” says IT Director Darin Adcock. “They e-mail and open attachments. They connect to our corporate network with their iPads to compose documents. We have a lot of confidential client information, and the ability to manage it all is key.”
Dowling Aaron’s bring-your-own-device program lets employees access corporate applications and data on their personal mobile computing devices. The Fresno, Calif., law firm was an early adopter, having embraced a BYOD strategy seven years ago.
The 125-employee law firm standardizes on desktop and notebook computers, but it lets lawyers connect their smartphones and tablets to the corporate network. Today, half the attorneys use Apple iPhones and the other half use Android smartphones. More recently, attorneys have begun purchasing tablets, mainly iPads, that they also use on the network.
“Mobility has really taken off,” Adcock says. “In the beginning, a couple of attorneys would be at lunch. One would be checking e-mail, and the other attorney would say, ‘Hey, what are you doing?’ If one attorney is doing it and better able to serve our clients, all the attorneys want it.”
To manage the devices, Adcock last fall turned to AirWatch’s cloud-based mobile device management (MDM) software to centrally configure, monitor and secure the devices. It lets him securely connect the devices to the corporate network and sync them to corporate e-mail. He can also enforce a more stringent password policy, encrypt data and remotely erase data if a device is lost or stolen.
“It’s protection of data,” he says. “We do a lot of contracts and have a lot of big clients, and the last thing we want is for people’s information or company secrets, like sales figures, to get out.”
Consumerization in the Workplace
Dowling Aaron, which has additional offices in Bakersfield and Visalia, adopted BYOD in 2005 when employees began bringing Palm Treos to work. Not long after, a new generation of consumer-oriented, feature-rich smartphones — the iPhone, Motorola Droid and other Android devices — pushed the Treos aside.
Today, Adcock sees a similar pattern happening with notebook computers as employees opt instead to tap their tablets for road duty rather than tote along their notebooks. Using their tablets, the lawyers can connect to the corporate network through a virtual private network, access corporate apps and data, as well as create and store documents through Microsoft Terminal Services.
Initially, security was not as robust as it is today. At first, Adcock required employees to password-protect their devices with a personal identification number (PIN), which was the only option available early on in the firm’s BYOD implementation.
But security practices became a chief focus for the firm in early 2011 after an attorney lost his tablet. Adcock says he quickly realized that his IT team needed to exert more control than just password protection over users’ devices to protect the firm’s data assets and that an enterprise solution was needed to centrally manage the growing number of devices.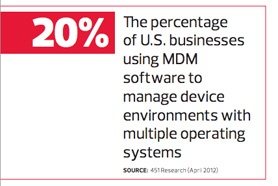
“It was a reality check,” he says. “At that moment, I realized that we needed to have the ability to remote-wipe the devices and not just PIN-protect them. Losing that tablet was the trigger to find a better solution to protect our devices.”
At the time, Dowling Aaron was using an e-mail synchronization app to remote-wipe the devices, but it was inconsistent. Sometimes the app would erase all the data. At other times, it would stop e-mail from syncing but still leave all the files on the devices. “It was not reliable,” Adcock says.
More granular control, including the option to erase only corporate data on employees’ devices without removing personal apps and data, was necessary. The solution the firm had begun using to manage users’ notebooks lacked a comparable capability for small-form-factor devices. That’s where the AirWatch cloud service came into play.
Onsite or in the Cloud?
After testing several product options, Adcock deployed AirWatch MDM in the fall of 2011 — opting for a cloud deployment over installing an appliance in the Dowling Aaron data center.
The AirWatch appliance has more features, including a secure gateway for e-mail. But the cloud service provides all the features the firm needs at about half the cost. After the initial purchase, the firm pays a minimal monthly fee per user.
When evaluating return on investment, it became clear that the firm didn’t have enough users to justify the hardware approach, Adcock says.

Photo: Cody Pickens
“We’re balancing the attorneys’ personal preferences with what is best for the firm,” says Darin Adcock, IT Director at Dowling Aaron.
Additionally, the cloud service requires no maintenance, which saves the IT staff time. “The less hardware in the server room, the better off we are,” he says. “It saves on physical space, saves on bandwidth and saves on energy.”
AirWatch is relatively easy to use too, he says. It took two days to set up the MDM software, creating security policies and connecting the app to the firm’s Microsoft Exchange Server implementation. Through a web-based console, Adcock can configure devices to authenticate and connect
to the firm’s Wi-Fi network in the office. With the MDM app, he also strengthened password protection, increasing the number of required characters. If a smartphone or tablet is lost or stolen, Adcock can now log on and do a partial or full wipe of the device. If an employee believes a device is only misplaced and will be found, Adcock can opt to erase only the corporate data, leaving any personal apps or data resident on the device.
But the firm’s BYOD policy does allow Adcock to erase all the data without employee approval if there’s any concern about theft or complete loss of a device.
“With BYOD, it gets touchy. It is their personal phone, so they’re storing pictures of their kids and other similar data,” he acknowledges. “What we say is that if you want to sync with the corporate network, you are giving us the ability to remove our data whenever we need to.”
To further boost security, Dowling Aaron uses AirWatch’s encryption capability to protect documents and e-mail on users’ devices.
From their desktop computers, attorneys can upload documents to AirWatch’s Secure Content Locker app. Both the app and the documents can then download to their mobile devices using industry-standard 256-bit encryption.
Meanwhile, a Secure Sockets Layer–encrypted tunnel protects in-transit e-mail.
In fact, the AirWatch tool makes it fast and easy for Dowling Aaron’s IT team to provision devices. To initiate the app, IT sends an e-mail link to a device. To initiate software installation, the user simply clicks on the link. The app then automatically prompts the user to create a PIN. After entering a user password to access e-mail, AirWatch syncs with Exchange.
“It was really easy to deploy, especially with the iPhone, because it has Exchange ActiveSync built in. It takes about five minutes to set up,” Adcock notes.
Android phones need more configuration work and require installation of a third-party e-mail application.
The ROI Advantage
For employees, BYOD programs often improve productivity and increase job satisfaction. They can also save businesses money.
For example, Dowling Aaron saves by allowing employees to use their personal mobile devices, but it spends about an equal amount on MDM software and employees’ monthly data plans. From an overall company standpoint, the MDM software does provide a good return on investment, Adcock says.
Watch Dowling Aaron's MDM Solution in Action
AirWatch ensures that employees conform to the company’s security policies. In the past, attorneys could turn off password protection once they left Adcock’s office. Now, the IT staff is alerted if that happens.
The technology also protects the company from data breaches and possible lost business that could result from them.
“You don’t know how much in future fees you may have lost if you are on the front page of the paper because of a data breach,” he says. “It could be a $100,000 or a $1 million. More important is the impact on your reputation; you can’t put a price on that.”
Ultimately, the company implemented BYOD not to save money but to give employees the flexibility to use devices of their choice. One year into its installation, the MDM software has proved to be worth the investment because it simplifies device management and provides the firm’s users with the peace of mind that data is protected.
“We’re balancing the attorneys’ personal preferences with what is best for the firm,” Adcock says. “AirWatch provides me with the flexibility to give users what they want — what they are most comfortable and productive with — and it allows me the capability to manage it from the IT side to make sure it’s secure.”










