Which Nation Takes Home the Gold in the Malwarelympics? [Infographic]
Combining the spirit of competition, teamwork, sportsmanship and country in one global sporting event, the Summer Olympic Games strives to bring out the best in humanity. On the flip side, malware aims to bring out the worst in technology. And some countries are harboring more malware than others.
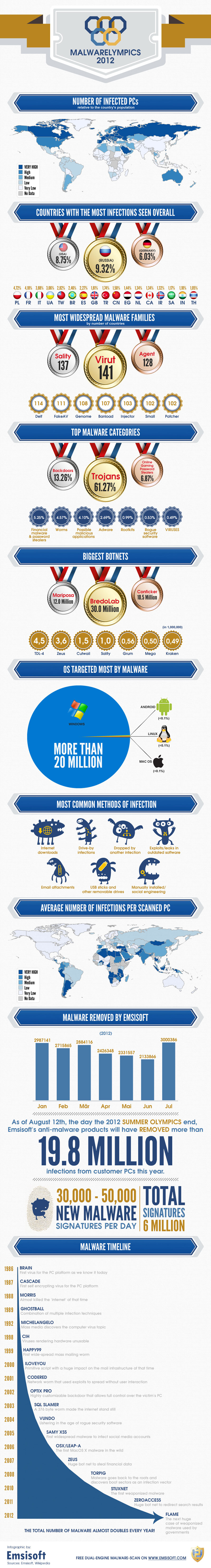
Emsisoft pulled together the data on malware proprietors in an infographic and broke it out by country for what it calls the Malwarelympics. In these games, winning the gold actually means you're losing. And according to the data, Russia wins the gold for the country with the most malware infections. The U.S. came in at number 2 for the silver and Germany is in third place, taking the bronze.
The state of malware across the globe is pretty staggering, but Emsisoft is on the job. According to the company's data, it has removed more than 19.8 million malware infections from PCs and creates 30,000-50,000 new malware signatures per day. At those rates, it would appear that malware breeds even faster than roaches.
Check out the full infographic on the Malwarelympics from Emsisoft below