MDM Makes BYOD a Blessing, Not a Curse
To paraphrase a popular proverb, IT and network administrators live in interesting times.
Fueled by the rise of mobile applications and BYOD initiatives, organizations have radically ramped up adoption of the latest smartphones and tablets to give users anywhere, anytime access to enterprise data. Those on-the-go users include everyone from high-ranking CEOs stationed at company headquarters to field service reps out on the front lines.
But what about the technology staff that must make this brave new mobile world manageable and secure? The policies and best practices for modern mobility playbooks are still being written while administrators develop rules on the fly and plug security leaks before cyberthieves exploit them.
Fortunately, IT teams don’t have to navigate this territory alone. Maturing technologies, along with security lessons carried over from traditional desktop computing environments, can help organizations gain control of their mobile operations.
“There are some new threats out there, but for the most part, they aren’t that different from what threatens other endpoint devices,” says Andrew Braunberg, research director of the business technology and software group for the analyst firm Current Analysis. “The real difference is scale.” Organizations are now grappling with many more mobile devices and operating systems than ever before.
To ensure that BYOD is a blessing and not a curse, mobility experts recommend a multilayered strategy using mobile device management (MDM), application management, security software and updated usage policies.
BYOD Is A Genie Out of the Bottle
Mobile management and security innovations are coming just in time. Users and organization managers like what they see from the BYOD trend. When staff members use the same mobile applications and types of mobile devices — even the same devices themselves — in their professional and personal lives, user satisfaction increases.
Staff members feel more comfortable using technology they have chosen. In addition, organizations can reap initial cost savings when fees for hardware and data plans shift to employees. This helps explain why some have already taken the BYOD plunge.
For example, technology leader Citrix Systems pays 15 percent of its employees a $2,100 stipend for mobile devices. Because employees must also purchase a maintenance contract to support the hardware, the Citrix help desk isn’t responsible for supporting employee-owned devices. Citrix says it is saving about $500 on each BYOD device over a three-year period. Other organizations adopting BYOD include Kraft Foods, CARFAX, Procter & Gamble, the Boulder Valley (Colo.) School District and the U.S. Department of Veterans Affairs.
“Forward-thinking IT managers are saying, ‘We’re jumping into BYOD because we realize from an internal perspective — and even from a competitive point of view — it’s the way to go,’” says Peter Frankl, vice president of lifecycle management at Absolute Software, a developer of MDM applications. “BYOD makes people more productive, and when it comes to recruiting talent, it allows companies to attract more advanced employees.”
But the rise of mobile workforces isn’t without significant tradeoffs. The trend also attracts thieves seeking to exploit new security openings that may result. The recently published McAfee Threats Report: First Quarter 2012 shows how significant the malware threat for mobile devices has become.
The research found 8,000 mobile malware samples in one quarter, an increase of more than 1,200 percent over the previous quarter. The Android OS accounts for almost 90 percent of the threats, with the majority of the breaches stemming from third-party app clearinghouses. (Similar security problems, however, weren’t associated with the official Android marketplace.)
“Android is an open platform, and it’s flexibility provides the opportunity for security holes,” says Nathan Jenniges, director of enterprise mobile security products for security software developer McAfee.
What happens when malware infects a smartphone or tablet? “Someone can take the binary file for a popular app, add some bad stuff and then distribute it from multiple app stores,” warns Brian Duckering, senior manager of enterprise mobility at Symantec.
Rooting or jailbreaking mobile devices can also expose users to malware threats. The malware infections gain access to low-level commands in a device’s operating system, which allows cybercriminals to circumvent many of the standard security controls built into the core software. “Once a device has been rooted, any application essentially has administrative access to the file system,” Jenniges says. “It can look at another app’s data or enable keylogging software that can capture keystrokes.”
MDM Is the Prescription for Mobile Risks
Security risks challenge network managers and IT administrators to safely deliver on the promise of mobility and BYOD. To cope, many are using a multilayered strategy that starts with MDM, which employs a combination of policies and technologies for protecting mobile hardware.
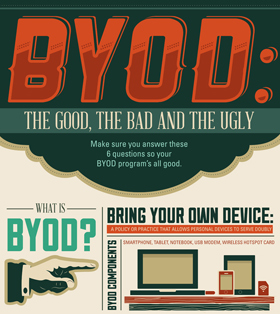
Beauty and the BYOD
Learn more about how your organization can deploy a smart, secure BYOD plan that makes mobility a more beautiful experience for all in our infographic.
“MDM gives you a baseline of device security, regardless of the mobile operating systems, hardware or applications,” Braunberg says.
Standard MDM features help IT administrators:
- Enforce the use of passwords and encryption on devices
- Establish virtual private networks (VPNs) for secure data transmissions to and from organization networks
- Remotely wipe data from hardware that’s been lost or stolen
- Protect the network from devices infected with malware
- Allow only approved applications to access data
IT managers typically use MDM to apply controls across mobile hardware and software platforms via a central administration console. New solutions are taking centralization to an even higher level. To reduce the complexity of using multiple optimization tools, some of the latest MDM solutions integrate with traditional system management tools already in use for PCs and Macs.
“From the same pane of glass, you can see PCs and Macs, plus Android, iOS, BlackBerry and Windows mobile devices,” Duckering says. “The advantages are that you reduce your technology footprint, minimize the incremental costs and leverage other organizational investments that may already be in place.”
Another MDM development is the wider variety of deployment choices available to network and IT administrators. For example, AirWatch offers its MDM solution as software as a service, a traditional on-premises implementation or as a turnkey software appliance preconfigured with the customer’s desired settings. AirWatch customers can easily transition from one model to another as their mobility and business needs change and evolve, says Matt Carrier, AirWatch’s director of product strategy.
Additional MDM Safety Measures
Although MDM serves as a cornerstone of mobile management and security, don’t stop with device management. “It’s just one piece of the puzzle,” Braunberg says. That’s because MDM can fall short when it comes to advanced security capabilities. For example, MDM controls may force users to enter a password before accessing corporate resources, but it might not prevent them from carelessly distributing information once they’ve been authenticated.
IT managers have come to realize they may need to add application management — sometimes called mobile application management or MAM — to their security portfolios. The strategy applies added security controls to individual apps rather than focusing on the device. “So even if you’re running rogue software or a jailbroken device, the applications themselves can’t be penetrated,” says Brian Reed, chief product officer for BoxTone.
For example, with higher-level MAM controls in place, a user must enter a unique password for each enterprise application. In addition, the enterprise data can also be encrypted with its own security key, so even if an outsider jailbreaks his way past the hardware encryption barrier, the mission-critical information stays safe.
BoxTone also provides an encrypted VPN tunnel between designated applications and data center servers to secure communications in transit. Other targeted security MAM measures could include settings that automatically remove corporate data on a device when a user closes out of a secured application or that prevent cutting, pasting and sharing of sensitive files. In the boundary-crossing world of BYOD, MAM also can apply such controls without inhibiting the device owner’s access to Facebook, personal photos or consumer-oriented apps.
MAM offers one other advantage: IT managers can secure what needs to be protected while avoiding undue tampering with the personal use of the devices. “No end user in their right mind is going to subject a device that they’ve paid for to extreme controls like disabling their camera or limiting access to app stores,” Duckering says.
Many organizations also use network access controls (NAC) to assess the security of devices connected to enterprise networks. In addition to providing authentication capabilities, NAC can also dynamically assess the security posture of wireless devices. It can block devices from connecting to the enterprise network if they lack appropriate security controls, such as antivirus software with updated signatures, a current and patched version of a supported operating system or a functioning host firewall.
The judicious use of MDM, MAM and NAC will create a foundation for a future where mobility will likely become even more engrained in business activities, Braunberg predicts. He suggests looking to the healthcare industry for a glimpse of how mobility may change the ways employees and organizations interact: Traveling nurses now capture patient vital signs in home settings and send the information to centralized databases using mobile devices.
This information flow, from the field to data centers, reverses what’s most common today. The change will increase the pressure on network and IT administrators to secure endpoint devices and communication channels, Braunberg says.
Interesting times, indeed.