Symantec: Flashback Trojan Authors Made $10,000 per Day
When news hit that Macs were being targeted by the Flashback Trojan, some users were shaken by the reality that what has largely been a safe computing ecosystem was now in the cross hairs of malware agents.
The motives behind hacking and malware vary, but more often than not, the goal is to make money. This is usually achieved by credit card or electronic banking theft, or by facilitating click fraud on online ads.
Symantec’s experts have delved into the Flashback Trojan code to put together any evidence that might point to a motive. What they found was an ad-clicking scheme at work. An official post from the Symantec blog reveals the details:
The Flashback ad-clicking component is loaded into Chrome, Firefox, and Safari where it can intercept all GET and POST requests from the browser. Flashback specifically targets search queries made on Google and, depending on the search query, may redirect users to another page of the attacker's choosing, where they receive revenue from the click . (Google never receives the intended ad click.)
The ad click component parses out requests resulting from an ad click on Google Search and determines if it is on a whitelist. If not, it forwards the request to the malicious server in the following form:
HTTP://[FLASHBACK_DOMAIN]/SEARCH?Q=[QUERY]&UA=[USER AGENT]&AL=[LANG]&CV=[VERSION]
Flashback uses a specially crafted user agent in these requests, which is actually the clients universally unique identifier (UUID) encoded in base64. This is already sent in the "ua" query string parameter, so it is likely that this is an effort to thwart "unknown" parties from investigating the URL with unrecognized user-agents.
The response is RC4 decrypted and then base64 decoded to reveal:
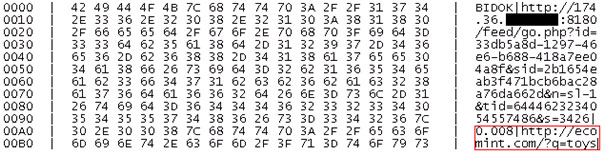
This hijacked ad click is based on a user searching for "toys". BIDOK is one of at least 5 commands that the Flashback expects to receive in response. However, for the ad-clicking component, this is the one we are interested in.
We can clearly see a value of 0.8 cents for the click and the redirection URL highlighted in red. This redirected URL is subsequently written into the browser so that the user is now directed to the new site, in effect hijacking the ad click Google should have received.
Based on a previous analysis, Symantec estimates that this click fraud activity potentially racked up $10,000 a day in revenue for the malware proprietors. This news comes after three fake antivirus programs were said to have generated $130 million in revenue. Clearly, the business interests of the malware underworld are not to be underestimated.










