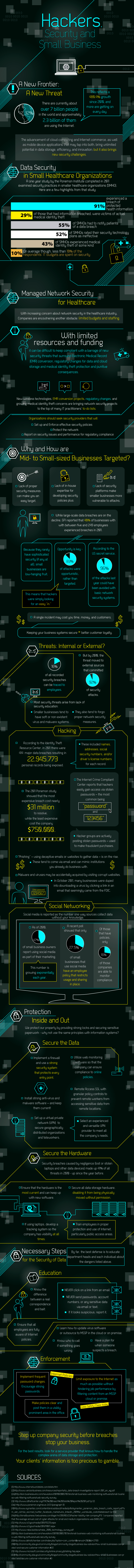
Hackers Have Their Eye On Small Business [Infographic]
When news breaks out about major security breaches on big organizations, it's easy to assume that it'll never happen to you, as a small business owner. After all, surely there are much bigger fish to fry.
But small businesses are in many ways the perfect target for hackers. Many SMBs don't bother to comply with the most basic of security measures and many don't have the IT resources in place to thwart the incoming attacks.
MegaPath, a data and IT security firm, put together an infographic on the security breach landscape for small and medium-sized businesses, which should serve as a warning to any small business owner. Security breaches can happen to any organization of any size, so don't take your data protection for granted.
Here are a few highlights from the MegaPath infographic:
- 91 percent of small healthcare organizations experienced a breach, according to a 2011 Ponemon Institute study
- 40 percent of businesses with 5 to 249 employees experienced a breach
- 96 percent of attacks could've been avoided with basic network security measures
- 22,945,775 personal records were exposed in 2011
- $31 million was the cost to clean up the most expensive security breach in 2011
Check out the full infographic from MegaPath below