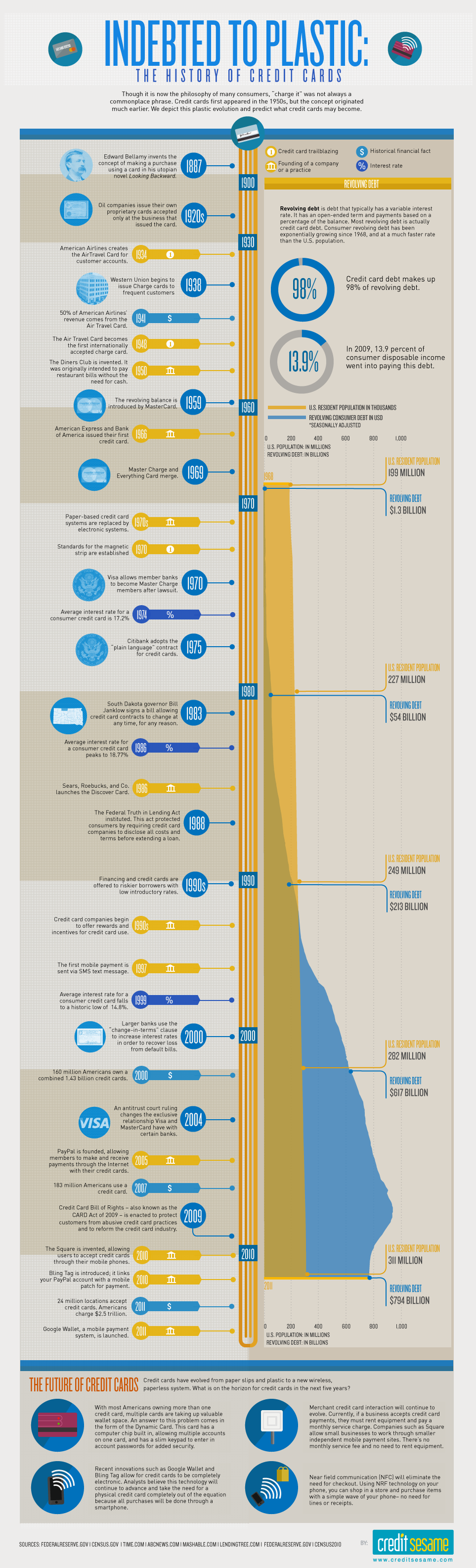
A Visual History of the Credit Card
If you're one of the many who've ditched cash in favor of credit or debit cards, you are not alone.
While payment by credit/debit card is ubiquitous today, it's actually a relatively modern marvel. Making its debut back in the 1950s, the credit card has increasingly become the default form or payment for consumers as it beats cash on several points.
First, it weighs less. Carrying a credit/debit card with $1,000 on is a lot easier than carrying around $1,000 in actual bills.
Second, it's traceable. Credit card payments produce statements that can tell you exactly the time and place of where you made your purchase. With cash, your only option is to hold on to your paper receipt, which as we all know, are easily lost or discarded.
Third, it's more secure. If a hacker gets a hold of your credit card information, the bank can freeze the card to prevent further purchases and work with the cardholder to refund any fraudulent charges. If a thief gets a hold of your cash, however, good luck recovering the funds.
Credit Sesame, a loan aggregator, compiled the data on the history of credit cards into a useful infographic.