Encryption Demystified
Just hearing the word "encryption" can bring shudders to technology professionals, many of whom find themselves intimidated by this seemingly incomprehensible technology. Perhaps the term conjures up scenes from the movie A Beautiful Mind, in which the brilliant Princeton mathematician John Forbes Nash filled chalkboards with unintelligible mathematics in an attempt to break cryptographic ciphers. Fortunately, you don't need a Ph.D. to understand applied cryptography. With a little basic background knowledge, you can use this powerful technology to protect confidential information.
There are three common ways that businesses use cryptography to protect sensitive information: encrypting web traffic, encrypting files and documents, and encrypting entire computers. We'll take a look at each of these after a brief overview of encryption technology.
What Is Encryption?
Encryption is a fairly simple concept: the transformation of information (otherwise known as the plaintext) into a form (called the ciphertext) that is unintelligible to anyone who does not possess the correct key. Decryption is the reverse process and uses a key to transform the ciphertext back into the readable plaintext. Presumably, only the intended recipient has the correct key, ensuring the confidentiality of the message.
When using encryption, the sender and recipient must use the same mathematical technique (known as an algorithm) to perform the encryption and decryption. Encryption algorithms can be divided into two groups: symmetric and asymmetric, which differ in the way the encryption keys are used.
- In symmetric algorithms, the sender uses a shared secret key to encrypt the message. The recipient must then use the same shared secret key to decrypt the message. Symmetric cryptography is very fast, but requires every possible pair of users to have a unique key. In a large system, the number of keys required can very quickly become unmanageable.
- In asymmetric algorithms (also known a public-key cryptography), the sender and recipient use related but different keys to encrypt and decrypt the message. Each participant has a pair of keys (one public and one private), and everyone has access to everyone else's public key. When a sender wants to encrypt a message, he or she does so using the recipient's public key. The recipient can then decrypt that message using his or her private key. Asymmetric cryptography is slower than symmetric cryptography, but key management is greatly simplified.
That's the nickel tour of encryption, and honestly, it's all you need to know to understand basic cryptographic applications. Of course, if you're interested there's a tremendous amount of mathematical detail behind these algorithms, and many books on the subject.
Encryption and the Web
Every Internet user encounters encryption on a daily basis — through the Hypertext Transfer Protocol Secure (HTTPS). As you probably know, standard web traffic uses plain old HTTP to transit the Internet. This protocol leaves an individual's web browsing open to interception as the data crosses the open Internet "in the clear" without the confidentiality benefits of encryption. If you run a web server and plan to engage in activities that deal with sensitive information, such as online banking or electronic commerce, you should definitely make sure that your site offers users the option (if not the requirement) of using encrypted HTTPS connections.
To enable HTTPS encryption on your site, you'll need to purchase an SSL certificate from a Certificate Authority (CA) and install it on your web server. There are many vendors offering these certificates, including VeriSign, Thawte and Go Daddy. The digital certificate contains a copy of your website's public encryption key along with a statement from the CA vouching for the key's authenticity to protect both you and your users from imposter websites (see Figure 1).
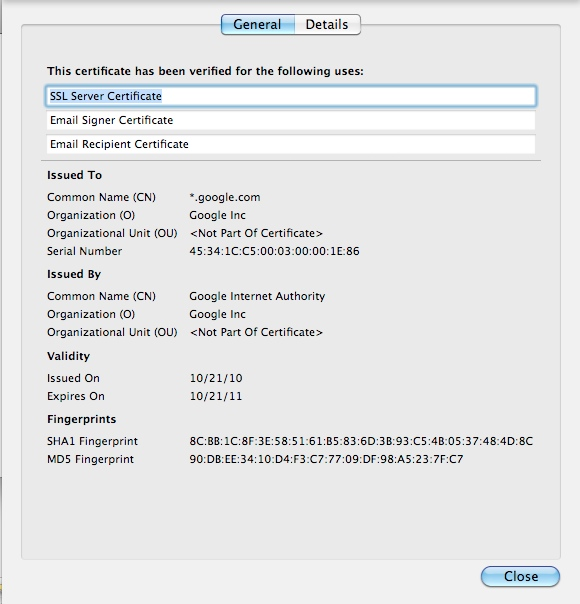 Figure 1: An example of the digital certificate used by Google's encrypted site
Figure 1: An example of the digital certificate used by Google's encrypted site
Users who wish to access your website securely simply type the URL into their browser with the familiar https:// prefix. Following a standard process, the browser then:
- Contacts the web server and requests a copy of the digital certificate.
- Verifies the authenticity of the certificate using information provided by the CA.
- Creates a shared secret key for symmetric encryption and encrypts it with the server's public key.
- Transmits the encrypted secret key to the web server.
When the web server receives the encrypted secret key, it decrypts it using the web server's private key, and then both systems use the shared secret key for all future communication.
At this point, you might ask yourself why the browser and server don't simply use asymmetric encryption for the entire communication. This would, after all, be much less complicated than the arrangement HTTPS uses, which involves the use of asymmetric encryption to exchange a symmetric encryption key. The underlying reason for this is that symmetric encryption runs at a much faster rate than asymmetric encryption, so this complex approach is actually more efficient for both the client and server.
Encrypting Files and Documents
You can also use encryption to protect individual files and documents, both while they are stored on a hard drive or removable media; and while they are in transit via e-mail, the web or other means. Fortunately, this process is much simpler than the complex mechanism used by HTTPS for encrypting web traffic. Typically, users select symmetric encryption for this type of encryption and use passwords to facilitate access to the encrypted file. There are many ways that you can encrypt individual files, such as:
- Using the built-in encryption functionality of many office productivity applications (for example, Microsoft Office 2010 offers the strong AES-256 algorithm for the encryption of password-protected files).
- Using a compression utility that offers encryption (the popular WinZip application for Windows offers strong encryption capabilities, as does the BetterZip application for the Mac).
- Installing a dedicated encryption utility that specializes in encrypting any type of file (the GnuPG package is a free implementation of the PGP encryption algorithm for Windows, Mac and Unix/Linux).
Using a file encryption solution will protect the file from unauthorized viewing or modification as long as the encryption key is kept in the hands of authorized users.
Encrypting Computers
The downside to using encryption on a per-file basis is that users need to remember to encrypt every confidential file that they create. While this is possible, it's also burdensome if users regularly work with confidential information. Many organizations supplement per-file encryption solutions with whole-disk encryption products that automatically encrypt all of the data stored on a hard drive. Full-disk encryption solutions operate in a manner that is completely transparent to the end user. Once a user logs into a computer with an authorized account and password, the disk-encryption drivers automatically decrypt data as it is requested.
Many operating systems come with some form of volume or full-disk encryption built-in, such as Microsoft Windows' BitLocker and the Mac OS X FileVault. Users may also select from a large number of commercial or open source encryption packages, including the popular free package TrueCrypt, available for Windows, Mac and Linux systems.
One very important fact to remember when dealing with disk-based encryption is that it only protects data while it is stored on the disk without an authorized user logged into the system. This is great protection against theft of a mobile computer, but it provides no protection for files that are copied off of the computer or accessed while an authorized user is on the system.
Encryption is a powerful technology — and, once you know how it works, an approachable technology — that provides tremendous benefits to any organization handling confidential information.










