The Do’s and Don’ts of Email Signature Creation [#Infographic]
In the digital age, the email signature has become just as important as the company letterhead.
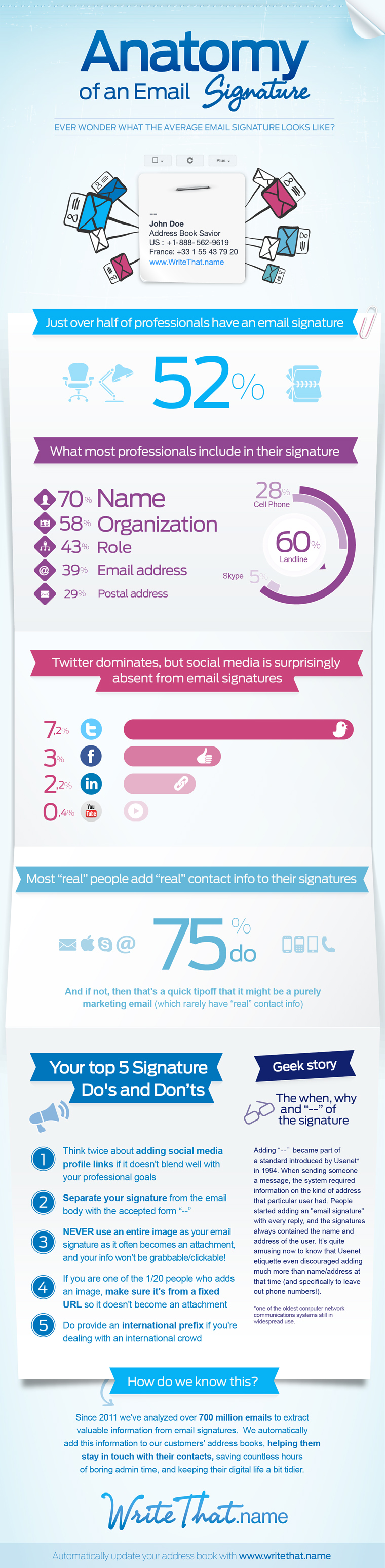
A new infographic from WriteThat.name takes a look at the do’s and don’ts of creating and implementing email signatures.
Fifty-two percent of professionals include an email signature with every outgoing email they send, whether to a client or colleague, according to the research compiled by WriteThat.name. It can help maintain a consistent impression in all of your digital business correspondence.
However, it can be tricky to get the recipe right. Email signatures should be concise, but not too boring. They need to strike a balance of providing relevant contact information without distracting from the content of your email.
The research also found that despite the ubiquity of cell phones, 60 percent of professionals still list their landline as a contact number versus 28 percent who use their cell phone.
Overall, social media is surprisingly absent. Only 7.2 percent of professionals list Twitter accounts, while an even lower 2.2 percent include their LinkedIn profiles.
Some professionals like to get fancy with an all image signature, which most experts don’t advise. An image signature can often become an attachment, which will increase the email file size and risk being blocked by a firewall.
Check out the full infographic below for more information.