How Many Vulnerabilities Does Your POS System Have? [#Infographic]
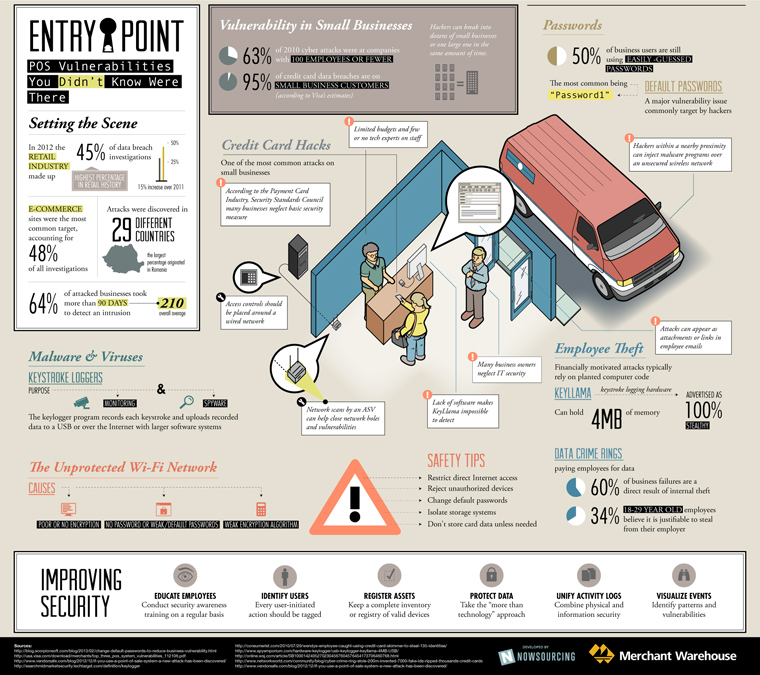
Too many small and medium-sized businesses overlook the potential IT security booby-traps that exist in their physical and virtual environments. By ignoring these security loopholes, businesses risk suffering devastating malware disasters.
Exactly how big is the SMB security issue? According to estimates by Visa, 95 percent of the data breaches in 2011 were from its small business customers.
A new infographic from MerchantWarehouse.com takes a look at some of the ways an insecure point-of-sale system can potentially expose SMBs’ corporate and customer data to attack.
For example, hackers can sit in a van outside of the business and inject malware into an unsecured wireless network.
Another major risk businesses face comes from employees. According to the data compiled in the infographic, 60 percent of “business failures” are attributed directly to internal theft.
Additionally just like consumers, many businesses rely on predictable and obvious passwords to secure their devices and networks. Survey data shows that 50 percent of business users are still using simple passwords like “Password1.”
Check out the full infographic below for more information.