Examining the Rise of Touch-Screen Technology
In the battle to conquer computers, touch-screen technology is the Trojan horse used by mobile computing to sneak in under the desktop’s radar and launch a takeover of PC users.
In a sign of the times, shipments of PCs dropped 14 percent worldwide in the first quarter of 2013, according to IDC. Global shipments of mobile phones, meanwhile, reached 1.6 billion in 2012, according to Strategy Analytics.
Mobile computing has become so dominant that its paradigms now influence desktop computers. Just look at the growing number of tablet/notebook hybrids or desktop computers with built-in touch-screen technology.
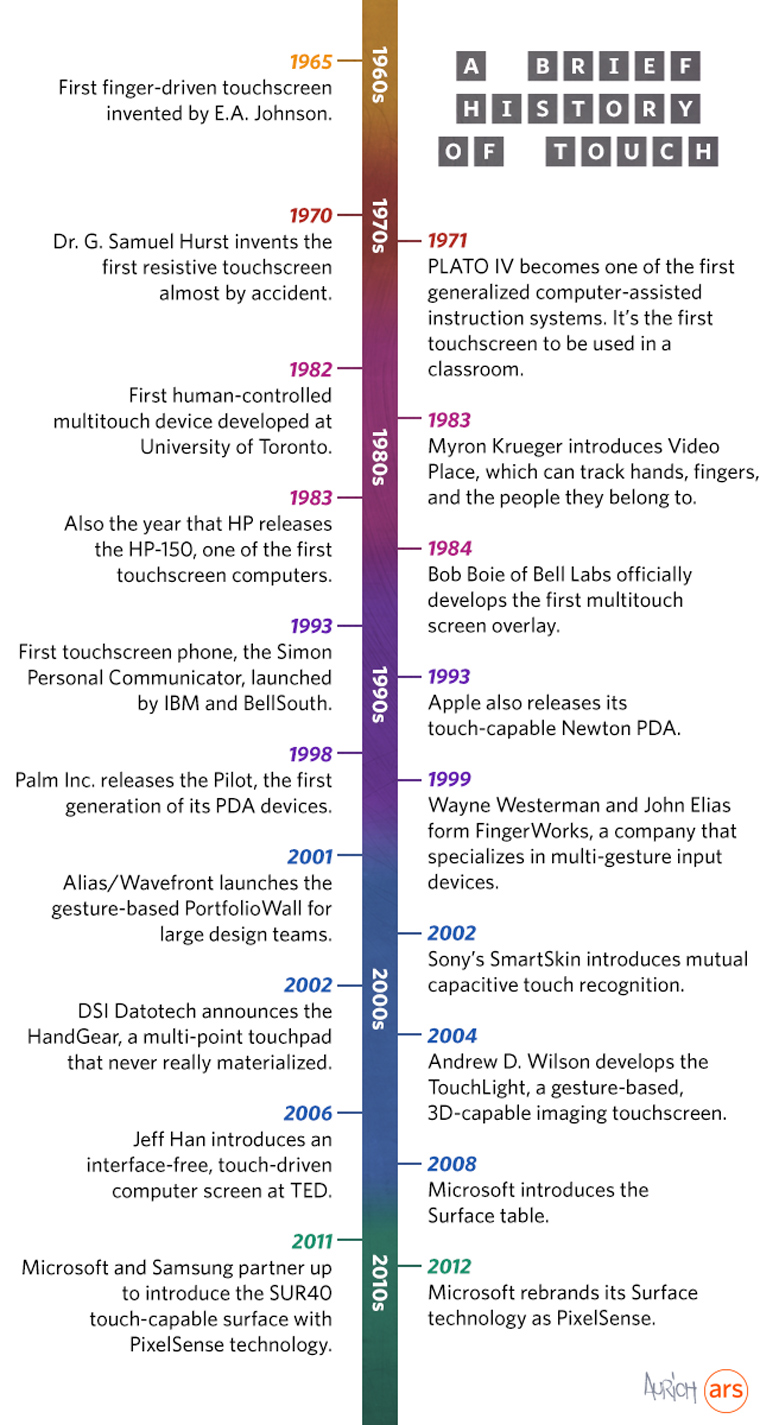
The path to transforming touch-screen technology from fiction to fact has been a long haul. The 50-year journey started in 1965, when the first finger-driven touch screen was invented by E.A. Johnson, as Ars Technica notes in its history of touch-screen technology. It took nearly another 30 years before IBM and BellSouth unveiled the Simon Personal Communicator in 1993.
Take a look at Ars Technica’s historical chart of touch-screen technology, below.