Ultrabooks with Intel Core vPro Processors Secure All the Way to the Chip [#Infographic]
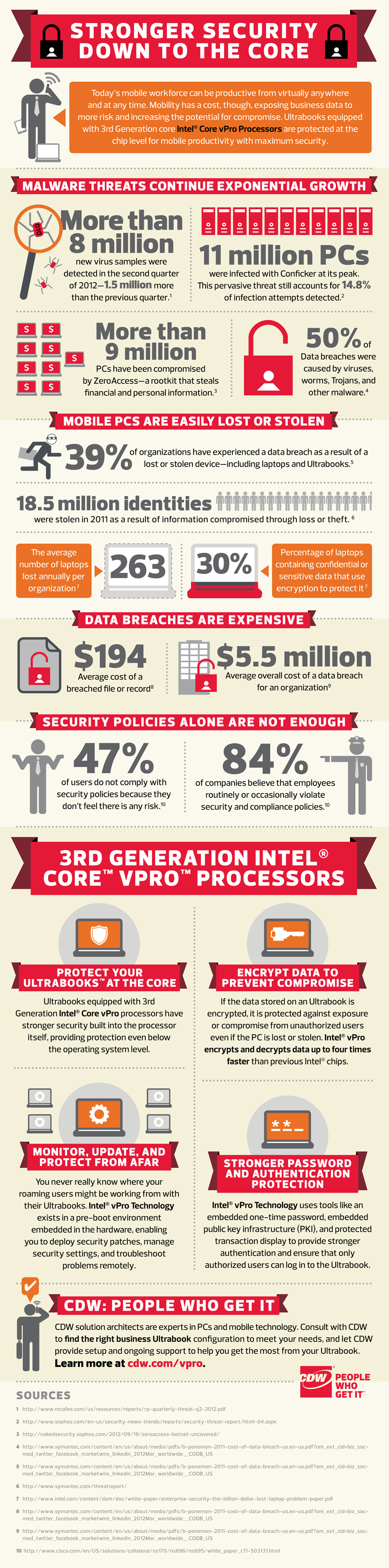
When it comes to security on a PC, most users probably think first of some form of antivirus software. Now, Intel has moved beyond software, drilling deeper for its latest security innovations.
A new line of ultrabooks, a special segment of high-end thin notebooks that Intel has defined, are equipped with third-generation Intel Core vPro Processors, which boast built-in security features at the chip level.
According to an infographic from CDW and Intel, some of the features include security management in a pre-boot environment, embedded public key infrastructure and an encryption process that works up to four times faster than previous Intel chips.
Check out the full infographic from CDW below.