No Data Is Safe with Cyber-Grinches on the Loose [#Infographic]
When we think about the meanest, nastiest sourpuss of the holiday season, Dr. Seuss’ Grinch probably comes to mind.
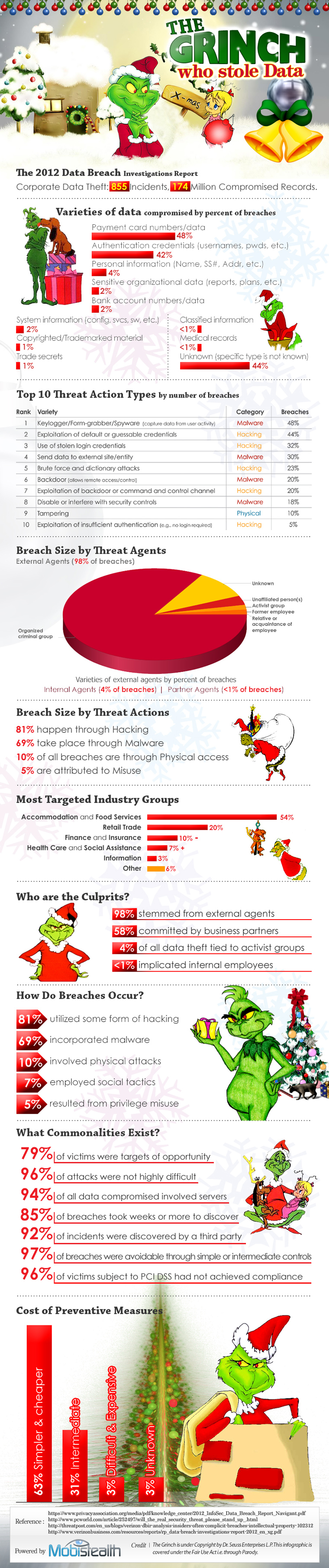
In that spirit, the folks at Mobistealth rounded up information and research on security breaches committed in 2012 by cyber-grinches intent on packing up corporate data in a big red bag and sneaking off into the night. Among the top 10 methods cyber-grinches used to steal data were spyware, stolen login credentials, brute force and remote access.
While hacktivist groups such as Anonymous have gained a lot of attention because of their exploits, they’re hardly the big bad wolves of hacking. According to Mobistealth’s data, organized crime groups were responsible for the overwhelming majority of breaches.
Hospitality and food-service businesses were the biggest targets of malware proprietors, accounting for 54 percent of the data breaches in 2012. This proves that every business really is in the technology business, whether they like it or not, because data is the new gold.
This holiday season, businesses should give themselves the gift of security. According to Mobistealth’s infographic, 63 percent of the breaches could have been prevented if simple and affordable security measures had been in place; only 3 percent of the breaches required difficult and expensive methods.
Check out the full infographic on the grinches who stole data, below.