Born to Be Wild: Young Professionals Exhibit Risky Tech Behavior [Infographic]
When it comes to technology, many young professionals are playing the game by their own rules. From the looks of it, they largely operate under rules that either (a) don’t exist or (b) could be called risky.
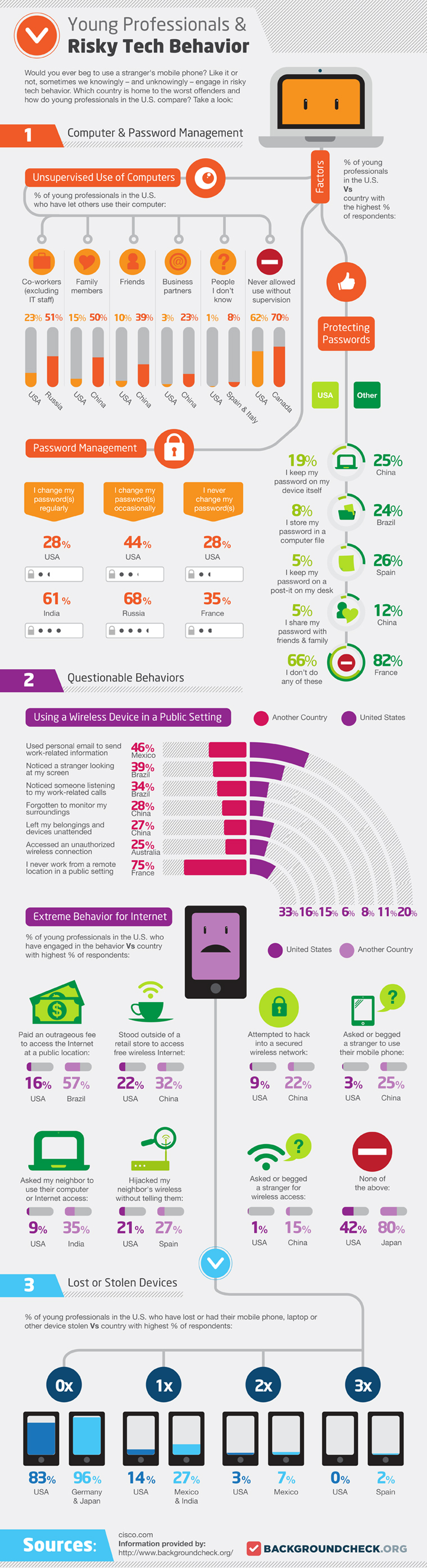
According to an infographic published by backgroundcheck.org, sharing passwords, using personal e-mail to send work-related information and hacking into secure wireless networks are just a few of the risky tech behaviors young professionals indulge in.
But how do young professionals in America compare with their peers across the globe?
The results are actually not as bad as you may think — but they’re also not as good as they should be.
According to survey results, only 1 percent of young professionals in America would allow a stranger to use their computer without supervision, compared with 8 percent of young professionals in Spain and Italy.
For 5 percent of young professionals in America, a Post-it note on their desk is their idea of password management. But it’s worse in Spain, where 26 percent of young professionals do the same.
There is even more damning evidence that password mismanagement is an epidemic: Only 28 percent of young professionals in America change their passwords regularly, compared with 61 percent of young professionals in India.
Aside from lax password security, the riskiest behavior exhibited by young professionals in America is using personal e-mail to send work-related information. Twenty percent of American young professionals do this; 46 percent of young professionals in Mexico do.
Want to learn more about the risky tech behavior of young professionals across the globe? Check out the full infographic below.