Are PINs Really Secure? [Infographic]
Passwords and secret codes aren’t just the stuff of James Bond movies — these days, everyone has multiple identifiers for secure access to bank accounts, e-mail, voicemail, Facebook and dozens of other personal data accounts.
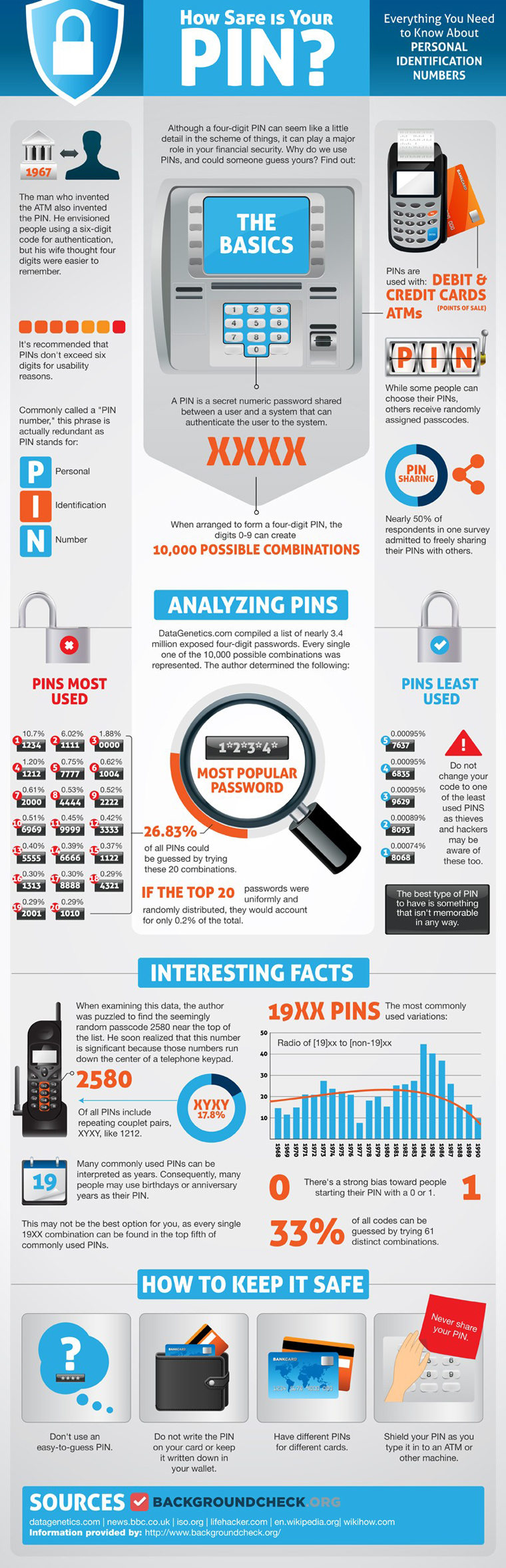
The Personal Identification Number (PIN) used with credit and debit cards and at ATMs is perhaps the oldest personal password. Invented in 1967 by the man who invented the ATM, the PIN was originally conceived as a six-digit number until the inventor’s wife changed his mind by convincing him that four numbers would be easier for people to remember.
Easier, maybe, but not necessarily secure. Incredibly, data from 10,000 exposed four-digit passwords showed that the most popular PIN combination was 1234. Furthermore, many users choose PINs that signify special dates, such as anniversaries or birthdays — making 19xx a very popular (and unsafe) combination.
For a more in-depth look at the history of PINs and what you need to know to keep your PIN safe, check out this infographic from Backgroundcheck.org: