The Dirty Little Secrets of Enterprise Mobility [Infographic]
More mobile, more problems. With workers free to get more work done on the road, companies are facing the woes of managing enterprise mobility. This includes ensuring that employees adhere to data and text plans and follow mobile security best practices in line with the company's mobile device management policy.
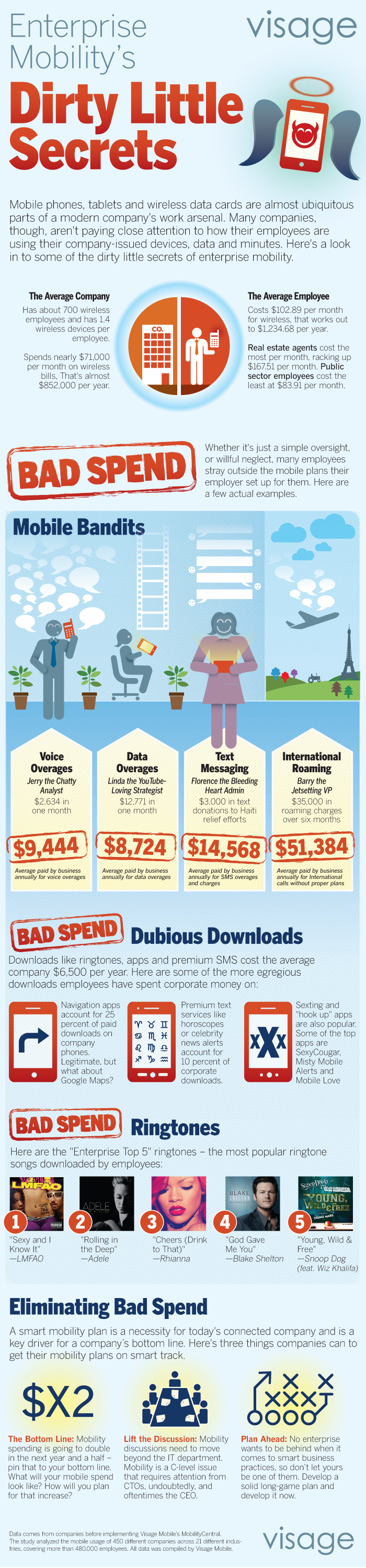
But as we know, not everyone is always on their best behavior. Some workers have been sneaky little devils and Visage, a mobile device management company, has tracked some of the naughty behavior of workers from 450 businesses for an infographic.
While the data and voice overages are sinful, the naughtiest transgression is perhaps the fact that LMFAO's "Sexy and I Know It" was number 1 on Enterprise Mobility's Top 5 Ringtones, with Rihanna's "Cheers (Drink to That)" and Snoop Dogg and Wiz Khalifa's "Young, Wild and Free" also making the list. Sounds the people working at these companies know how to throw a good happy hour.
Here are a few highlights from the Visage's findings:
- $9,444 is the average amount that businesses paid in voice overages.
- $8,724 is the average amount that businesses paid in data overages.
- $51,384 is the average amount that businesses paid in international roaming fees.