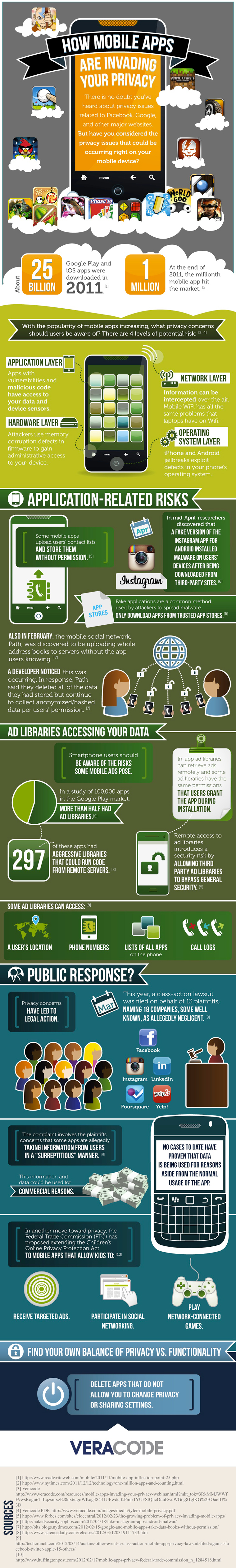
The Security Vulnerabilities of Mobile Apps [Infographic]
The poster child for modern Internet privacy woes is probably Facebook, the king of social networks. The young company has been taken to task several times over its multiple privacy changes and faces a recently filed class-action lawsuit alleging privacy violations.
The proliferation and rise of the mobile-app economy, however, has ushered in a new crack in the user privacy wall.
Mobile applications are user-friendly silos that offer users a focused purpose and feature set. But they’re also potential targets for privacy violations.
Because mobile apps are so personalized and live on a user’s device, there can be a false sense of security. But, as with anything web-based, privacy is a relative concept.
Veracode put together some data on the user-privacy threats of mobile apps in an infographic. Some of the highlights from the visualization include:
- Some mobile apps upload and store users’ contact information without permission.
- Fake and impostor applications can trick users into downloading malware.
- Remote access to ad libraries allows third-party ad libraries to bypass general security.
Check out the full infographic from Veracode, via Mashable, below.